New 0Day Hack Attack Alert Issued For All Windows Users
With 84 security issues requiring fixing, Microsoft's monthly Patch Tuesday patch rollout is upon us. While only four of these security vulnerabilities are classified by Microsoft as critical in nature, one does stand out for requiring your most urgent attention.
What is the CVE-2022-22047 Windows 0Day?
CVE-2022-22047 is, Microsoft confirms, already being exploited by attackers. Microsoft describes this 0Day security threat as a Windows client-server runtime subsystem (CSRSS) elevation of privilege vulnerability. Almost every version of Windows is vulnerable to this threat, including Windows 7, 8.1, 10, 11, and Windows Server 2008, 2012, 2016, 2019, and 2022. Perhaps surprisingly, CVE-2022-22047 isn't given a critical rating by Microsoft but an important one instead.
Is this a critical Windows vulnerability or not?
Not everyone agrees with this classification. "Windows CSRSS Elevation of Privilege, tracked as CVE-2022-22047, is critical because it is actively exploited in the wild," says Mike Walters, co-founder of Action1, a cloud-based monitoring specialist. "It has a 7.8 CVSS score because it can only be executed locally," Walters continues, adding that "use of this vulnerability gives an attacker SYSTEM privileges." Although the technical details are understandably sparse at this point in time, Walters warns that when paired with other attacks, it could give complete control of a Windows endpoint.
According to a Zero Day Initiative analysis of this latest Patch Tuesday security update, CVE-2022-22047 is precisely the type of vulnerability that is "typically paired with a code execution bug, usually a specially crafted Office or Adobe document, to take over a system."
CISA orders federal agencies to patch
Another indicator of how serious this 0Day exploit should be taken comes from the Cybersecurity & Infrastructure Security Agency (CISA). It has just added CVE-2022-22047 to its Known Exploited Vulnerabilities Catalog. This requires that federal agencies in the U.S. now have until 2 August to patch their systems. This doesn't mean you are off the hook if not a federal agency yourself. CISA adds that it "strongly urges all organizations to reduce their exposure to cyberattacks by prioritizing timely remediation of Catalog vulnerabilities as part of their vulnerability management practice."
A review of zero-day in-the-wild exploits in 2023
28 Mar 2024In 2023, Google observed 97 zero-day vulnerabilities exploited in-the-wild. That’s over 50 percent more than in 2022, but still shy of 2021’s record of 106. Today, Google published its fifth annual review of zero-days exploited in-the-wild.
Read MoreVulnerability In 16.5K+ VMware ESXi Instances Let Attackers Execute Code
25 Mar 2024VMware has acknowledged the presence of several vulnerabilities in its products after they were privately reported.The company has released updates to address these issues in the affected software. While each vulnerability is rated as ‘Important,’ their combined potential impact escalates to ‘Critical’ severity. Shadowserver has tweeted a warning about vulnerabilities in VMware ESXi instances. These vulnerabilities can enable a malicious actor with local admin privileges to bypass sandbox protections. Shadowserver is conducting scans and sharing its findings to help mitigate the risks associated with these vulnerabilities.
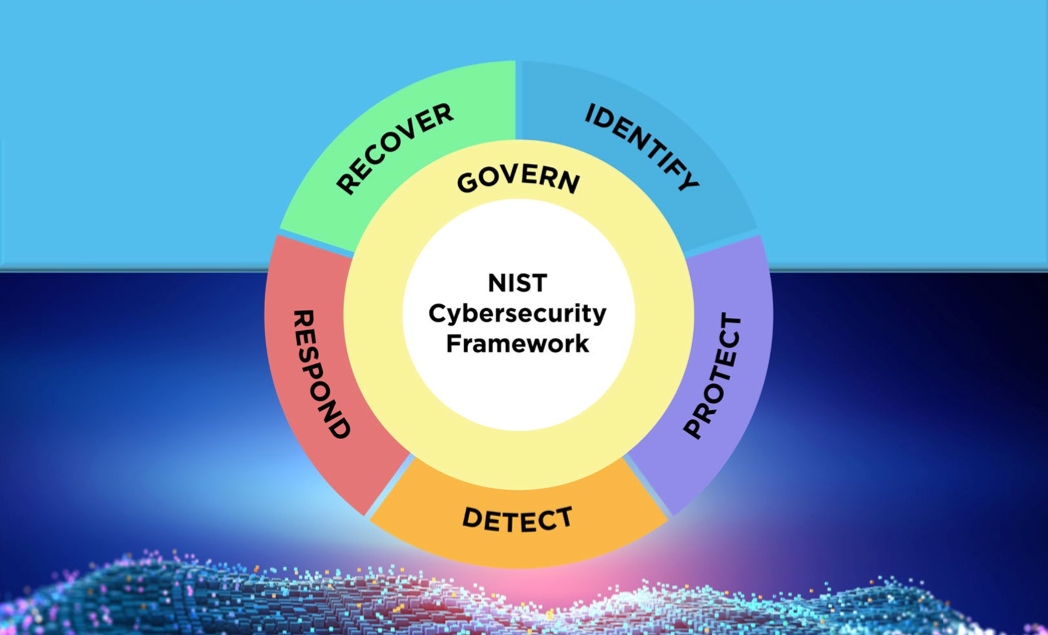
Read MoreNIST Cybersecurity Framework 2.0: 4 Steps to Get Started
20 Mar 2024The National Institute of Standards and Technology has revised the book on creating a comprehensive cybersecurity program that aims to help organizations of every size be more secure. Here's where to start putting the changes into action.
Read More