IceFire ransomware now encrypts both Linux and Windows systems
Threat actors linked to the IceFire ransomware operation now actively target Linux systems worldwide with a new dedicated encryptor.
SentinelLabs security researchers found that the gang has breached the networks of several media and entertainment organizations around the world in recent weeks, starting mid-February, according to a report shared in advance with BleepingComputer.
Once inside their networks, the attackers deploy their new malware variant to encrypt the victims' Linux systems.
When executed, IceFire ransomware encrypts files, appends the '.ifire' extension to the filename, and then covers its tracks by deleting itself and removing the binary.
It's also important to note that IceFire doesn't encrypt all files on Linux. The ransomware strategically avoids encrypting specific paths, allowing critical system parts to remain operational.
This calculated approach is intended to prevent a complete system shutdown, which could cause irreparable damage and even more significant disruption.
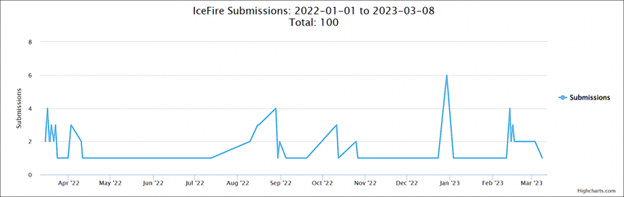
While active since at least March 2022 and mostly inactive since the end of November, IceFire ransomware returned in early January in new attacks, as shown by submissions on the ID-Ransomware platform.
IBM Aspera Faspex targeting
IceFire operators exploit a deserialization vulnerability in the IBM Aspera Faspex file-sharing software (tracked as CVE-2022-47986) to hack into targets' vulnerable systems and deploy their ransomware payloads.
This high-severity pre-auth RCE vulnerability was patched by IBM in January and has been exploited in attacks since early February [1, 2] after attack surface management firm Assetnote published a technical report containing exploit code.
CISA also added the security flaw to its catalog of vulnerabilities exploited in the wild on February 2021, ordering federal agencies to patch their systems until March 14.
"In comparison to Windows, Linux is more difficult to deploy ransomware against–particularly at scale. Many Linux systems are servers: typical infection vectors like phishing or drive-by download are less effective," SentinelLabs says.
"To overcome this, actors turn to exploiting application vulnerabilities, as the IceFire operator demonstrated by deploying payloads through an IBM Aspera vulnerability."
Shodan shows more than 150 Aspera Faspex servers exposed online, most in the United States and China.
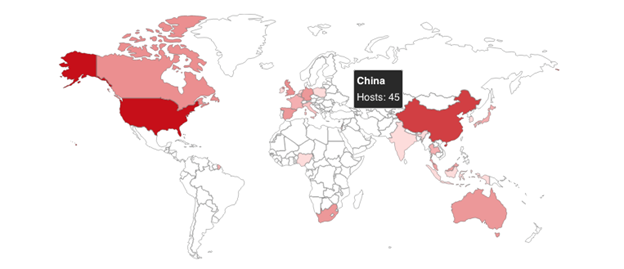
Internet-exposed IBM Aspera Faspex servers (Shodan)
Most ransomware strains encrypt Linux servers
IceFire ransomware's move to expand Linux targeting after previously focusing on attacking only Windows systems is a strategic shift that aligns with other ransomware groups that have also started attacking Linux systems in recent years.
Their move matches a trend where enterprises transitioned to Linux-powered VMware ESXi virtual machines, which feature improved device management and a lot more efficient resource handling.
After deploying their malware on ESXi hosts, the ransomware operators can use a single command to encrypt the victims' Linux servers en masse.
While IceFire ransomware doesn't specifically target VMware ESXi VMs, its Linux encryptor is just as efficient, as shown by victims' encrypted files submitted to the ID-Ransomware platform for analysis.
"This evolution for IceFire fortifies that ransomware targeting Linux continues to grow in popularity through 2023," SentinelLabs says.
"While the groundwork was laid in 2021, the Linux ransomware trend accelerated in 2022 when illustrious groups added Linux encryptors to their arsenal."
Similar encryptors have been released by multiple other ransomware gangs, including Conti, LockBit, HelloKitty, BlackMatter, REvil, AvosLocker, RansomEXX, and Hive.
Emsisoft CTO Fabian Wosar previously told BleepingComputer that other ransomware gangs (besides the ones we have already reported on), including Babuk, GoGoogle, Snatch, PureLocker, Mespinoza, RansomExx/Defray, and DarkSide, have developed and deployed their own Linux encryptors in attacks.
New HardBit Ransomware 4.0 Uses Passphrase Protection to Evade Detection
17 Jul 2024Cybersecurity researchers have shed light on a new version of a ransomware strain called HardBit that comes packaged with new obfuscation techniques to deter analysis efforts.
Read MoreIndonesia tightens cybersecurity after ransomware attack
15 Jul 2024The recent cyberattack in Indonesia, which massively disrupted its national data system, has urged the country to strengthen its cyber resilience and evaluate its digital technology policy, reported Xinhua.
Read MoreNew “Paste and Run” Phishing Technique Makes CTRL-V A Cyber Attack Accomplice
09 Jul 2024A new phishing campaign tries to trick email recipients into pasting and executing malicious commands on their system that installs DarkGate malware.
Read More

