Emotet Botnet Distributing Self-Unlocking Password-Protected RAR Files to Drop Malware
The notorious Emotet botnet has been linked to a new wave of malspam campaigns that take advantage of password-protected archive files to drop CoinMiner and Quasar RAT on compromised systems.
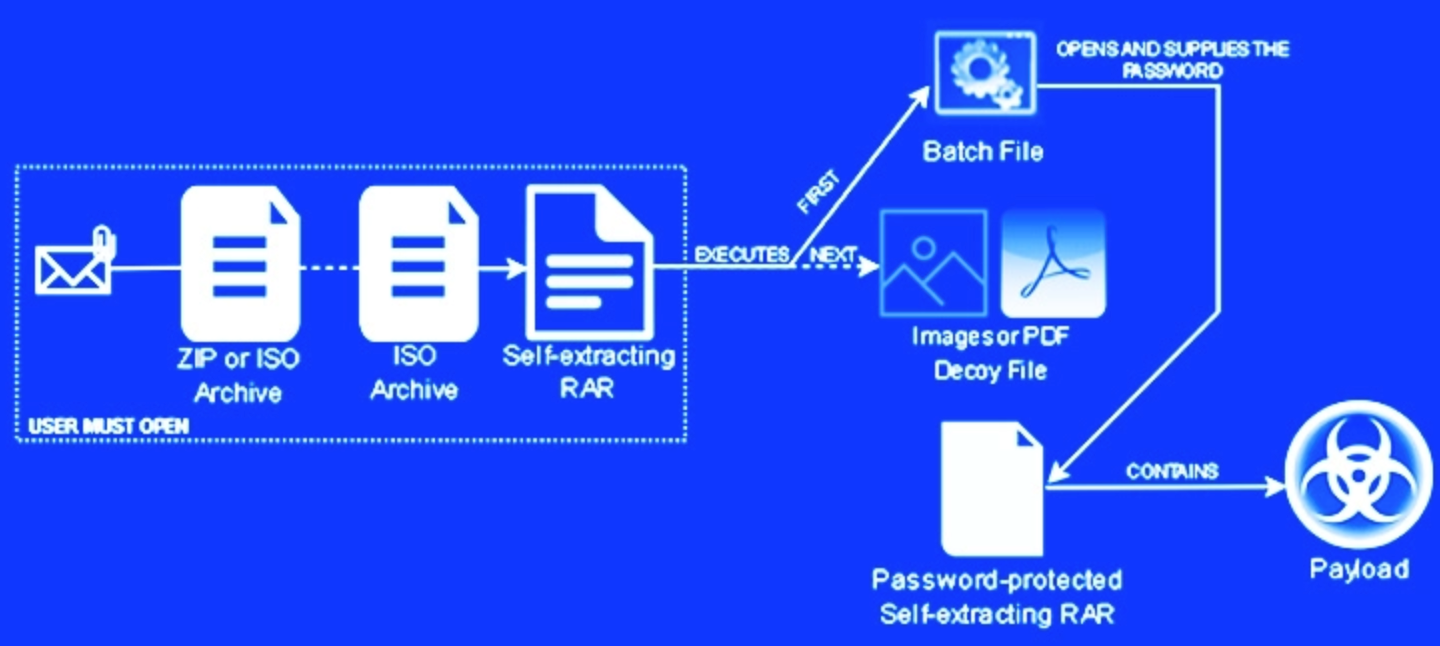
In an attack chain detected by Trustwave SpiderLabs researchers, an invoice-themed ZIP file lure was found to contain a nested self-extracting (SFX) archive, the first archive acting as a conduit to launch the second.
While phishing attacks like these traditionally require persuading the target into opening the attachment, the cybersecurity company said the campaign sidesteps this hurdle by making use of a batch file to automatically supply the password to unlock the payload.
The first SFX archive file further makes use of either a PDF or Excel icon to make it appear legitimate, when, in reality, it contains three components: the password-protected second SFX RAR file, the aforementioned batch script which launches the archive, and a decoy PDF or image.
"The execution of the batch file leads to the installation of the malware lurking within the password-protected RARsfx [self-extracting RAR archive]," researchers said in a Thursday write-up.
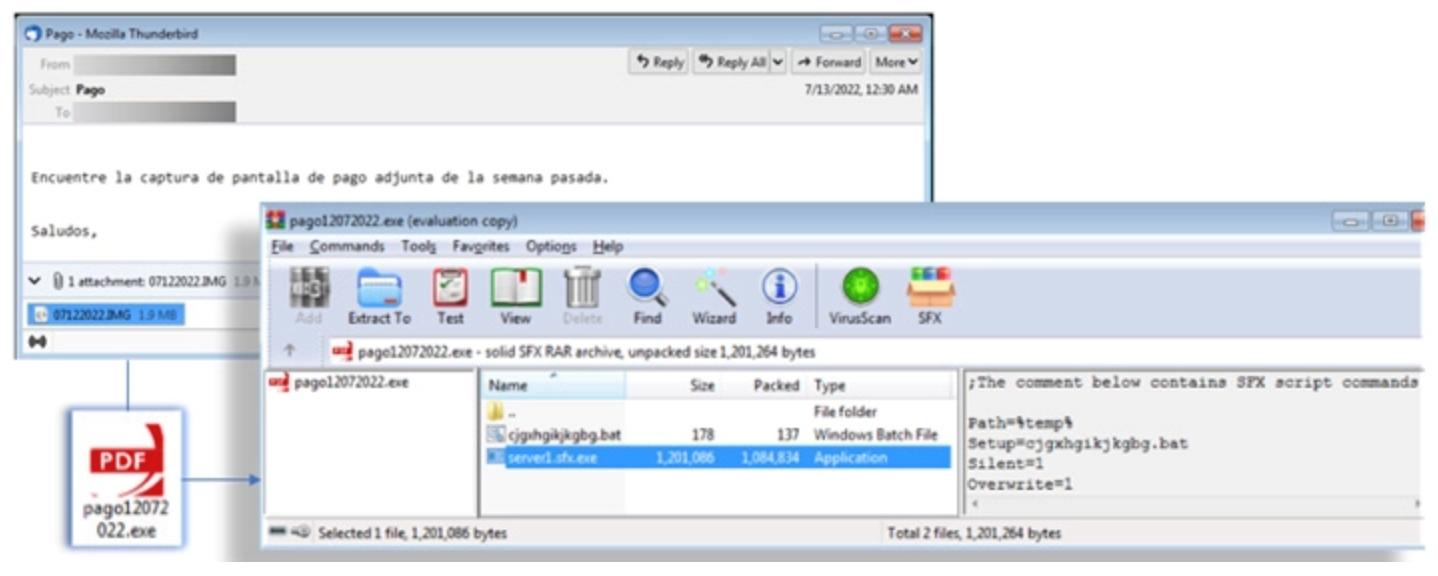
The batch script achieves this by specifying the archive's password and the destination folder to which the payload will be extracted, in addition to launching a command to display the lure document in an attempt to conceal the malicious activity.
Lastly, the infection culminates in the execution of CoinMiner, a cryptocurrency miner that can also double up as a credential stealer, or Quasar RAT, an open source .NET-based remote access trojan, depending on the payload packed in the archive.
The one-click attack technique is also notable in that it effectively jumps past the password barrier, enabling malicious actors to carry out a wide range of actions such as cryptojacking, data exfiltration, and ransomware.
Researcher said it has identified an increase in threats packaged in password-protected ZIP files, with about 96% of these being distributed by the Emotet botnet.
"The self-extracting archive has been around for a long time and eases file distribution among end users," the researchers said. "However, it poses a security risk since the file contents are not easily verifiable, and it can run commands and executables silently.
A review of zero-day in-the-wild exploits in 2023
28 Mar 2024In 2023, Google observed 97 zero-day vulnerabilities exploited in-the-wild. That’s over 50 percent more than in 2022, but still shy of 2021’s record of 106. Today, Google published its fifth annual review of zero-days exploited in-the-wild.
Read MoreVulnerability In 16.5K+ VMware ESXi Instances Let Attackers Execute Code
25 Mar 2024VMware has acknowledged the presence of several vulnerabilities in its products after they were privately reported.The company has released updates to address these issues in the affected software. While each vulnerability is rated as ‘Important,’ their combined potential impact escalates to ‘Critical’ severity. Shadowserver has tweeted a warning about vulnerabilities in VMware ESXi instances. These vulnerabilities can enable a malicious actor with local admin privileges to bypass sandbox protections. Shadowserver is conducting scans and sharing its findings to help mitigate the risks associated with these vulnerabilities.
Read MoreNIST Cybersecurity Framework 2.0: 4 Steps to Get Started
20 Mar 2024The National Institute of Standards and Technology has revised the book on creating a comprehensive cybersecurity program that aims to help organizations of every size be more secure. Here's where to start putting the changes into action.
Read More